Attack Surface Management
Continuous external exposure analysis with validated findings and internal context

Specular provides a continuously updated view of an organization’s internet facing services across on premise, cloud, and third party infrastructure.
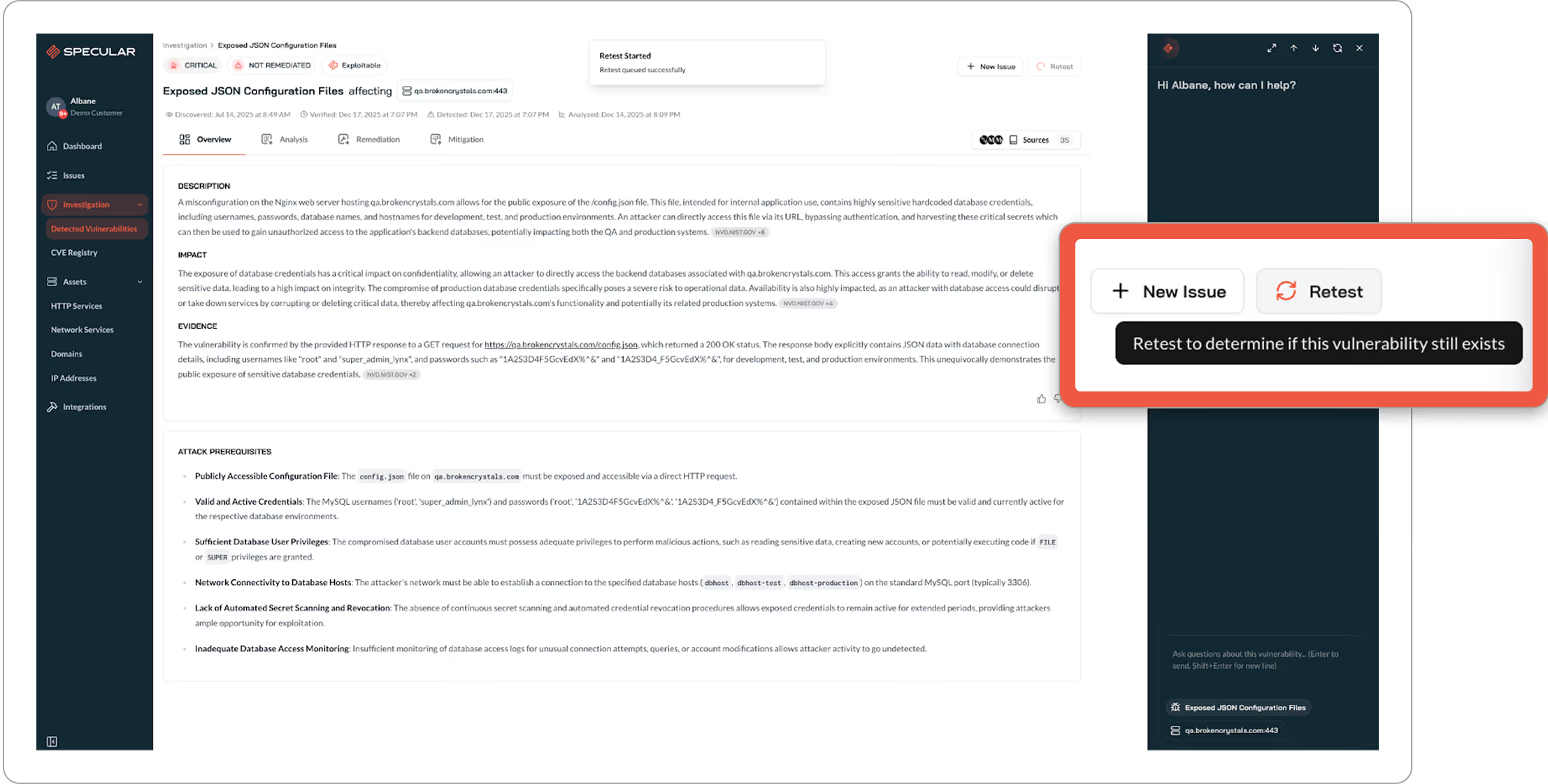
It identifies exposed assets, detects vulnerabilities and misconfigurations, and validates which findings are actually exploitable so teams can act with confidence.
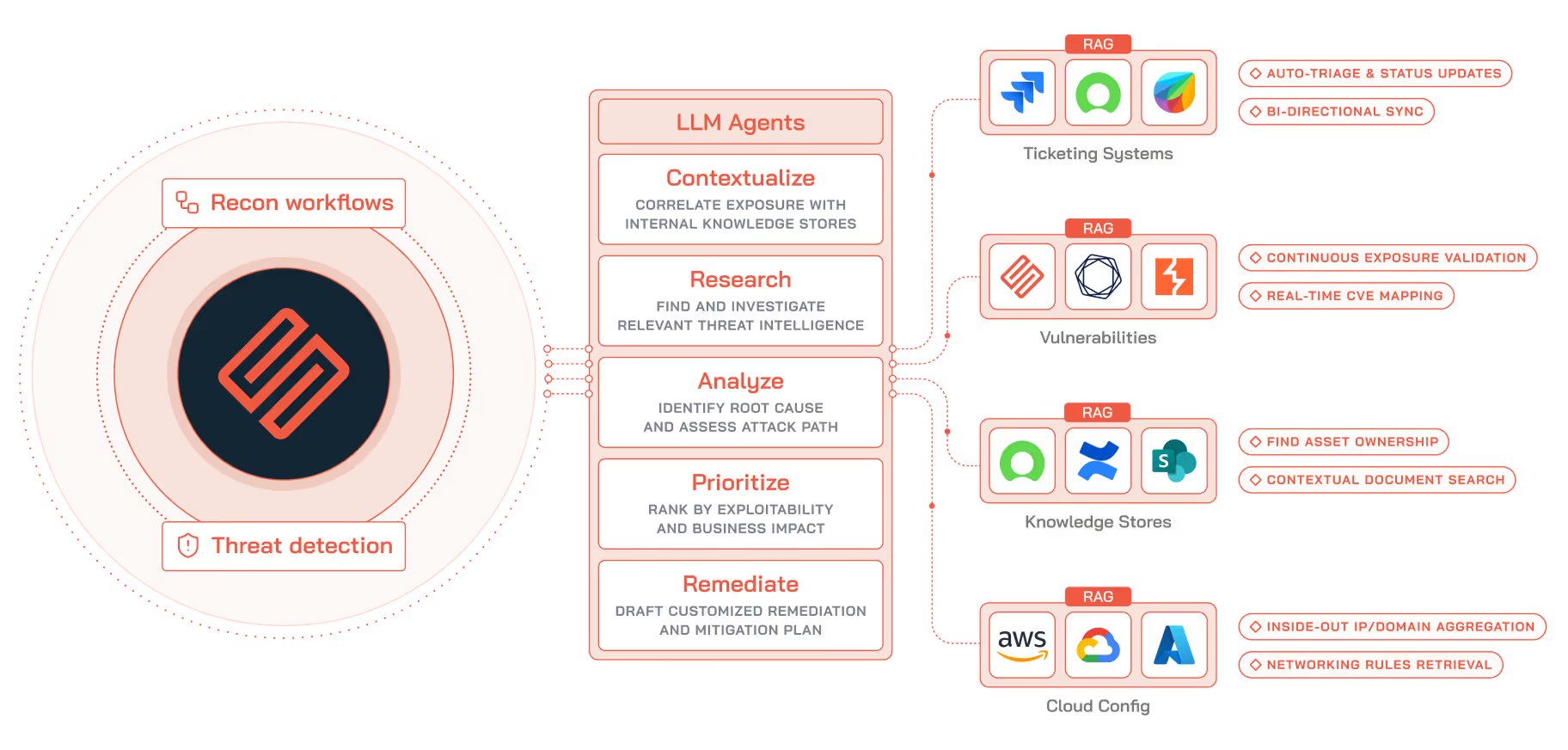
AI agents verify real world exploitability, enrich findings with internal context, and route fix ready guidance to the right team. Security teams move from exposure discovery to resolution without manual triage or repeated validation work
Why Traditional ASM Breaks Down
Most attack surface tools stop at discovery.
They inventory exposed assets but leave security teams responsible for validating exploitability, understanding impact, and deciding what action is required. That work is manual, inconsistent, and difficult to scale across environments, subsidiaries, and acquisitions.
Scanners generate large volumes of high severity findings.
At the same time, scanners generate large volumes of high severity findings with no confirmation of reachability or business relevance. Security teams spend days validating results, reproducing issues, and trying to justify remediation to engineering teams. Important exposures remain open while teams debate risk instead of fixing it.
Repeated Manual Validation
The result is repeated manual validation, slow handoffs to engineering and IT, and longer exposure windows for exploitable findings.
Continuous Visibility into External Exposure
Security teams typically turn to ASM to solve a small set of concrete problems:

CONTINUOUSLY MAINTAIN
Maintain an accurate, continuously updated inventory of all internet facing services spanning onprem, cloud, and third party, including shadow IT and short lived cloud services

IDENTIFY
Identify which vulnerability and misconfigurations are actually reachable and exploitable so engineering effort is spent on the right issues

SCALE
Scale visibility and assessment across subsidiaries, acquisitions, and hybrid onprem and cloud environments without increasing headcount

REMEDIATION
Streamline remediation through agentic workflows that optionally query your internal knowledge stores to generate customized analysis and remediation guidance
When ASM works, it changes outcomes:
Security teams can defend their posture with evidence, not assumptions
Exposure windows shrink because time is not lost to manual triage or internal debate
Engineering receives validated findings with remediation guidance and business context to act immediately
Senior security staff spend less time validating scanners and more time on architecture and risk strategy

Continuous External Analysis
Specular analyzes the external attack surface from an outside in perspective. AI agents continuously enumerate internet facing infrastructure and assess exposed services using workflows similar to external network penetration testing.
As environments change, new services, misconfigurations, and vulnerabilities are detected automatically. Findings are reviewed by Deep Research AI agents to confirm exploitability and relevance before being surfaced to security teams.
Why Specular Is Different
Analysis built for security decision making
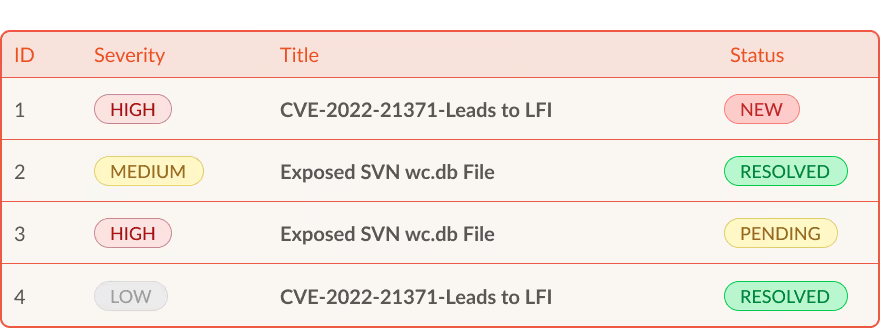
Deep Research AI agents produce customized analysis for each finding rather than generic severity scores. Agents examine live responses, request behavior, and asset metadata to confirm exploitability and scope.
Internal context from sources such as CMDBs, cloud metadata, and internal documentation is used to generate customized guidance based on how assets are deployed and managed. This allows security teams to prioritize based on real exposure and business impact without manual validation.

Faster assessment when time matters
When new vulnerabilities are disclosed, security teams need to understand exposure quickly.
Specular helps teams determine whether newly disclosed vulnerabilities affect their external attack surface, assess exploitability, and understand impact across all internet facing environments. This supports faster and more confident decisions during high risk disclosure events.


How It Works
Get a Closer Look with Specular
Specular helps turn findings into fixes.




