Continuous Threat Exposure Management
From external exposure to confirmed exploitability

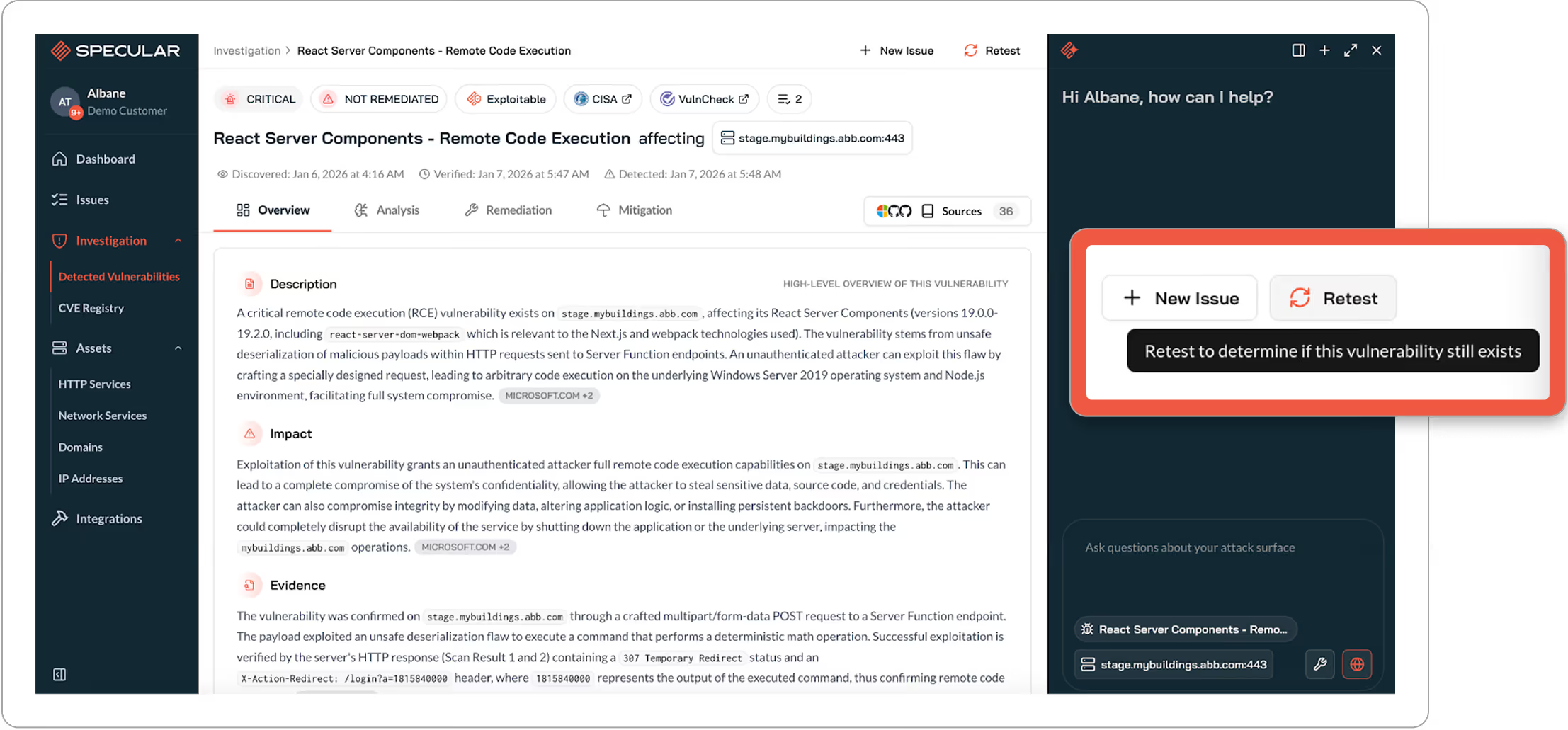
Specular gives security teams a continuous, attacker driven view of the external attack surface.
AI agents replace manual and episodic testing by continuously discovering exposed services, validating exploitability through live responses, and producing fix ready customized to exposure. Noise is filtered automatically so teams focus on exposures that matter now.
CTEM Breaks Down Between Assessments
Most CTEM programs still rely on snapshots or point-in-time assessments that are outdated the moment they are delivered.
Between tests, new shadow IT assets appear, configurations drift, and misconfigurations are introduced, leaving security teams blind to their current attack surface.
Scanners generate thousands of high severity CVEs without context.
At the same time, scanners generate thousands of high severity CVEs without context. Security teams spend days waiting for reports, then more time trying to reproduce findings, confirm reachability, and prove to engineers that an issue is actually exploitable.
A Live View of Exploitable Risk
Security teams running CTEM programs need to:

CONTINUOUSLY SEE
See the external attack surface the way an advanced persistent threat would

PRIORITIZE
Prioritize based on proven exploitability and impact, not CVSS scores or theoretical severity

REDUCE
Reduce time spent validating scanner output and reproducing findings

UNDERSTAND
Understand exposure across environments, subsidiaries, and business units

DELIVER
Deliver fix ready context directly into engineering workflows without becoming the bottleneck
Specular's Execution of the CTEM Lifecycle
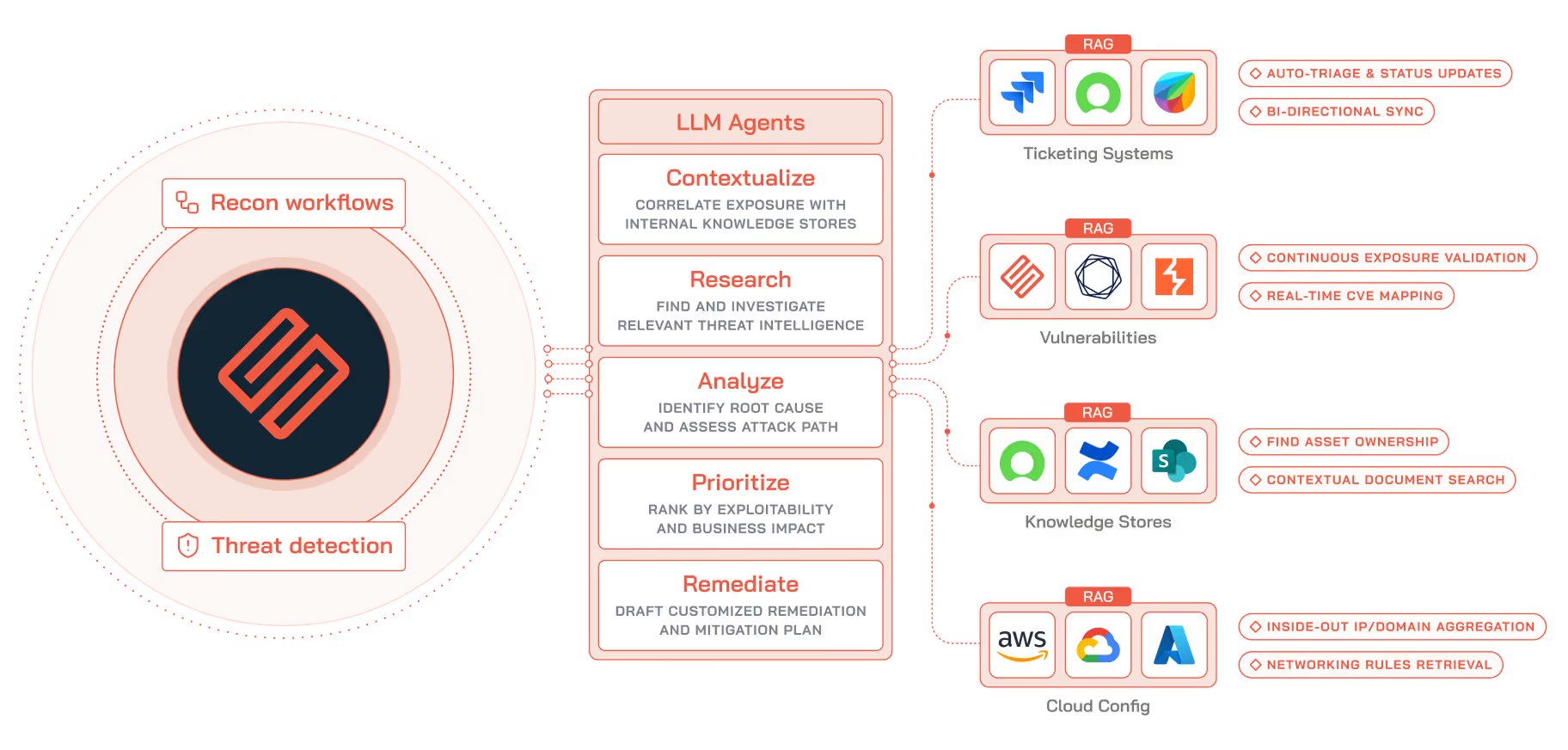
Specular leverages AI agents to continuously execute the CTEM lifecycle: scoping, discovery, prioritization, validation, and mobilization.
At the center of the system is an Intelligence Core powered by large language models, which coordinates a set of specialized agents to assess exposure as the environment changes.

Recon Agents
Recon agents continuously enumerate internet facing infrastructure, uncovering shadow IT and short lived cloud assets as they appear.

Discovery and Validation Agents
Discovery and validation agents attempt to replay requests, analyze responses, and parse asset metadata to confirm whether a vulnerability is reachable and exploitable in practice.

Remediation Agents
Remediation agents translate confirmed exploits into actionable tickets, producing clear, code level remediation steps that can be consumed by engineering teams.
Unlike human led tests that run sporadically, Specular’s agents operate continuously, applying attacker thinking while producing documentation suitable for engineering and security review.

Deep Research Agentic Workflows
Specular is built to support how security teams assess exposure.
Deep Research AI agents provide customized analysis for each finding. Agents examine live responses, request behavior, and asset metadata to help confirm exploitability and scope. Internal context such as CMDB data and documentation is referenced where available to reflect how assets are deployed and owned.
This approach helps security teams prioritize findings based on exposure and relevance rather than severity scores alone.
How It Works
Get a Closer Look with Specular
Specular helps turn findings into fixes.




